Connect private networks
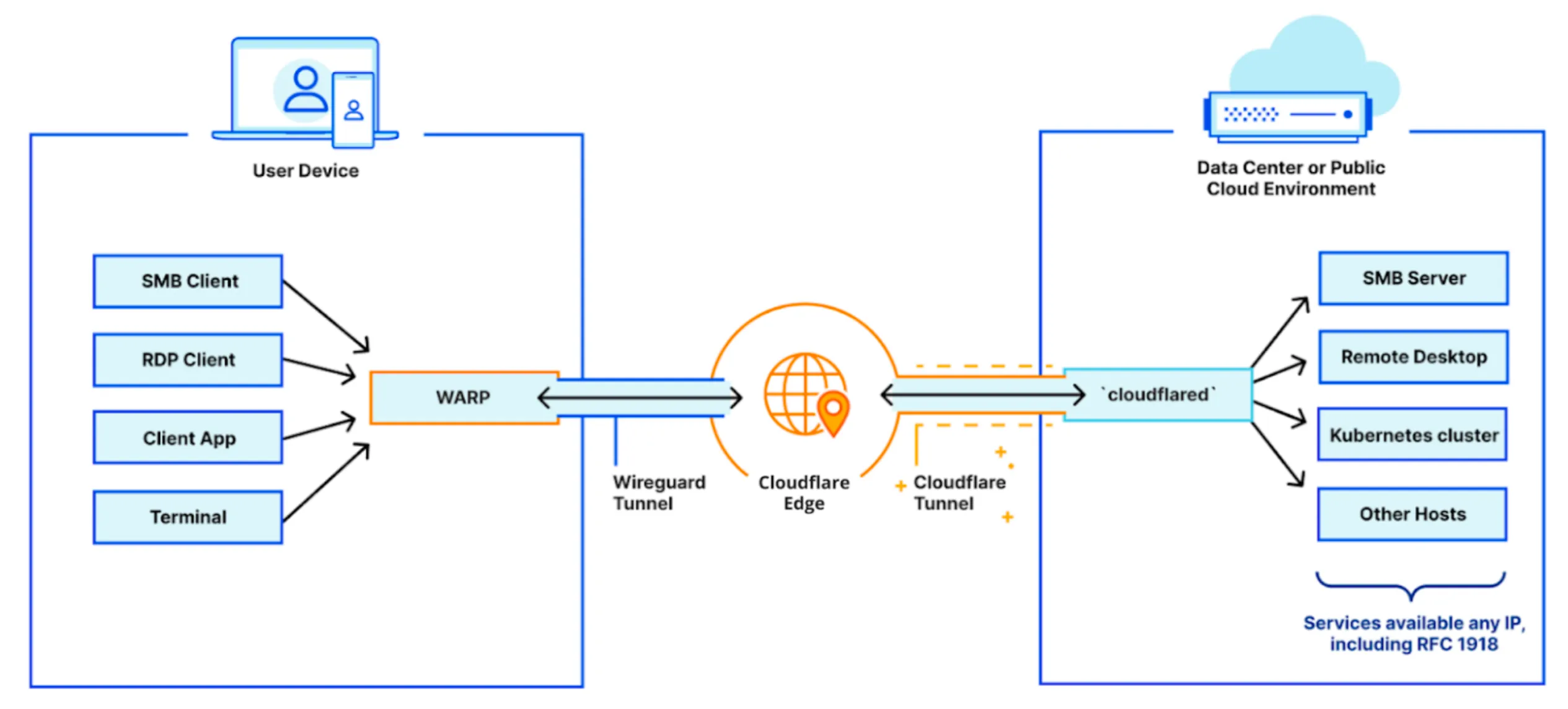
A private network has two primary components: the server and the client. The server’s infrastructure (whether that is a single application, multiple applications, or a network segment) is connected to Cloudflare’s global network by Cloudflare Tunnel. This is done by running the cloudflared daemon on the server.
On the client side, end users connect to Cloudflare’s global network using the Cloudflare WARP client. The WARP client can be rolled out to your entire organization in just a few minutes using your in-house MDM tooling. When users connect to an IP made available through Cloudflare Tunnel, WARP sends their connection through Cloudflare’s network to the corresponding tunnel.
To enable remote access to your private network, follow the guide below.
To connect your infrastructure with Cloudflare Tunnel:
-
Create a Cloudflare Tunnel for your server by following our dashboard setup guide. You can skip the connect an application step and go straight to connecting a network.
-
In the Private Networks tab for the tunnel, enter the IP/CIDR range of your private network (for example
10.0.0.0/8). This makes the WARP client aware that any requests to this IP range need to be routed to your new tunnel.
To connect your devices to Cloudflare:
- Deploy the WARP client on your devices in Gateway with WARP mode. The Cloudflare certificate is only required if you want to display a custom block page or filter HTTPS traffic.
- Create device enrollment rules to determine which devices can enroll to your Zero Trust organization.
By default, WARP excludes traffic bound for RFC 1918 space ↗, which are IP addresses typically used in private networks and not reachable from the Internet. In order for WARP to send traffic to your private network, you must configure Split Tunnels so that the IP/CIDR of your private network routes through WARP.
-
First, check whether your Split Tunnels mode is set to Exclude or Include mode.
-
If you are using Include mode, add your network’s IP/CIDR range to the list. Your list should also include the domains necessary for Cloudflare Zero Trust functionality.
-
If you are using Exclude mode:
- Delete your network’s IP/CIDR range from the list. For example, if your network uses the default AWS range of
172.31.0.0/16, delete172.16.0.0/12. - Re-add IP/CDIR ranges that are not explicitly used by your private network. For the AWS example above, you would add new entries for
172.16.0.0/13,172.24.0.0/14,172.28.0.0/15, and172.30.0.0/16. This ensures that only traffic to172.31.0.0/16routes through WARP.
- Delete your network’s IP/CIDR range from the list. For example, if your network uses the default AWS range of
By tightening the private IP range included in WARP, you reduce the risk of breaking a user’s access to local resources.
By default, all WARP devices enrolled in your Zero Trust organization can connect to your private network through Cloudflare Tunnel. You can configure Gateway to inspect your network traffic and either block or allow access based on user identity and device posture.
- Go to Settings > Network.
- Enable Proxy for TCP.
- (Recommended) To proxy traffic to internal DNS resolvers, select UDP.
- (Recommended) To proxy traffic for diagnostic tools such as
pingandtraceroute, select ICMP. You may also need to update your system to allow ICMP traffic throughcloudflared:
Linux
-
Ensure that
ping_group_rangeincludes the Group ID (GID) of the user runningcloudflared.- To get the Group ID of the user, run
id -g. - To verify the Group IDs that are allowed to use ICMP:
Terminal window sudo sysctl net.ipv4.ping_group_rangenet.ipv4.ping_group_range= 0 10000- Either add the user to a group within that range, or update the range to encompass a group the user is already in. To update
ping_group_range:
Terminal window echo 0 10001 | sudo tee /proc/sys/net/ipv4/ping_group_range - To get the Group ID of the user, run
-
If you are running multiple network interfaces (for example,
eth0andeth1), configurecloudflaredto use the external Internet-facing interface:Terminal window cloudflared tunnel run --icmpv4-src <IP of primary interface>
Docker
In your environment, modify the ping_group_range parameter to include the Group ID (GID) of the user running cloudflared.
By default the cloudflared Docker container ↗ executes as a user called nonroot inside of the container. nonroot is a specific user that exists in the base image ↗ we use, and its Group ID is hardcoded to 65532.
Cloudflare will now proxy traffic from enrolled devices, except for the traffic excluded in your split tunnel settings. For more information on how Gateway forwards traffic, refer to Gateway proxy.
You can create Zero Trust policies to manage access to specific applications on your network.
-
Go to Access > Applications > Add an application.
-
Select Private Network.
-
Name your application.
-
For Application type, select Destination IP.
-
For Value, enter the IP address for your application (for example,
10.128.0.7). -
Configure your App Launcher visibility and logo.
-
Select Next. You will see two auto-generated Gateway Network policies: one that allows access to the destination IP and another that blocks access.
-
Modify the policies to include additional identity-based conditions. For example:
-
Policy 1
Selector Operator Value Logic Action Destination IP in 10.128.0.7And Allow User Email matches regex .*@example.com -
Policy 2
Selector Operator Value Action Destination IP in 10.128.0.7Block
Policies are evaluated in numerical order, so a user with an email ending in @example.com will be able to access
10.128.0.7while all others will be blocked. For more information on building network policies, refer to our dedicated documentation. -
-
Select Add application.
Your application will appear on the Applications page.
End users can now reach HTTP or TCP-based services on your network by visiting any IP address in the range you have specified.
To check that their device is properly configured, the user can visit https://help.teams.cloudflare.com/ to ensure that:
- The page returns Your network is fully protected.
- In HTTP filtering, both WARP and Gateway Proxy are enabled.
- The Team name matches the Zero Trust organization from which you created the tunnel.
Check the local IP address of the device and ensure that it does not fall within the IP/CIDR range of your private network. For example, some home routers will make DHCP assignments in the 10.0.0.0/24 range, which overlaps with the 10.0.0.0/8 range used by most corporate private networks. When a user’s home network shares the same IP addresses as the routes in your tunnel, their device will be unable to connect to your application.
To resolve the IP conflict, you can either:
-
Reconfigure the user’s router to use a non-overlapping IP range. Compatible routers typically use
192.168.1.0/24,192.168.0.0/24or172.16.0.0/24. -
Tighten the IP range in your Split Tunnel configuration to exclude the
10.0.0.0/24range. This will only work if your private network does not have any hosts within10.0.0.0/24. -
Change the IP/CIDR of your private network so that it does not overlap with a range commonly used by home networks.